In 2026, cryptocurrency wallets remain the cornerstone of digital asset management. As crypto adoption continues to climb, these tools enable users to store, send, and receive tokens securely.
How Cryptocurrency Wallets Work: Software vs. Hardware Wallets Compared (2026 Edition)
In 2026, cryptocurrency wallets remain the cornerstone of digital asset management. As crypto adoption continues to climb, these tools enable users to store, send, and receive tokens securely. Yet, with over $3.4 billion stolen in hacks during 2025 alone, according to Chainalysis reports, understanding how cryptocurrency wallets function has never been more critical. This surge in thefts underscores the need for informed choices amid rising market volatility and regulatory scrutiny.
The topic matters now because blockchain technology is integrating deeper into finance. Fund managers and retail investors alike face expanding options, from decentralized finance (DeFi) protocols to tokenized real-world assets. Poor wallet choices can lead to irreversible losses. This article breaks down the essentials without hype, offering clarity on types, comparisons, and practices to safeguard your holdings.
Understanding Cryptocurrency Wallets
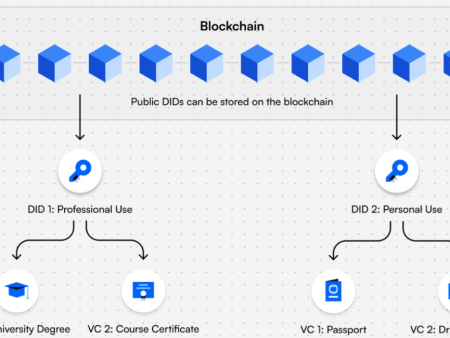
Cryptocurrency wallets are digital tools that manage private keys—unique codes granting access to your assets on the blockchain. Think of them as bank accounts for crypto, but instead of holding money, they store keys that prove ownership.
Hot vs. Cold Cryptocurrency Wallets
Hot wallets connect to the internet for quick access. They suit daily transactions but expose users to online threats. Cold wallets, by contrast, stay offline, reducing hack risks significantly.
Custodial vs. Non-Custodial Cryptocurrency Wallets
Custodial wallets, often provided by exchanges like Coinbase, handle keys for you. Convenient, yet they mean trusting a third party. Non-custodial options give full control, aligning with crypto’s ethos of self-sovereignty.
Simple analogy: A custodial wallet is like a bank vault where the bank holds the key. A non-custodial one is your personal safe at home.
Software Cryptocurrency Wallets Explained
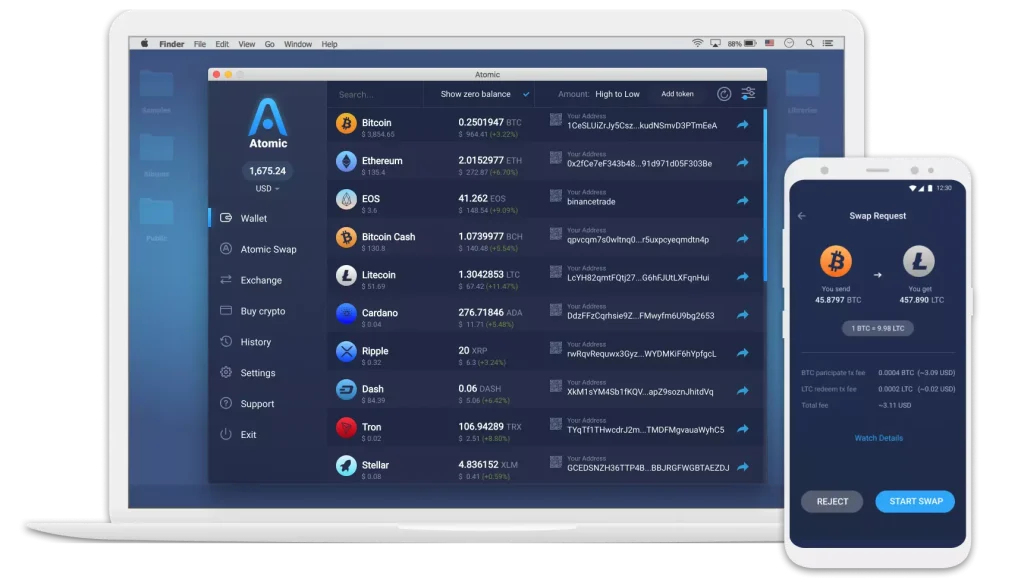
Software wallets run on devices like phones or computers. They include mobile apps (e.g., Trust Wallet), desktop versions (e.g., Exodus), and browser extensions (e.g., MetaMask).
These are typically hot wallets, ideal for active trading. Setup is straightforward: Download the app, generate a seed phrase (a 12-24 word backup), and fund it via an exchange transfer.
However, they rely on device security. If malware infects your computer, keys could be compromised.
Cryptocurrency Wallets: Guide
Hardware Cryptocurrency Wallets Explained
Hardware wallets are physical devices, such as Ledger Nano or Trezor Model T, storing keys offline. They sign transactions without exposing keys to the internet.
Consider them fortified USB drives. When transacting, connect the device to a computer; it approves actions securely.
Hardware options excel in cold storage, making them preferred for long-term holdings. Prices range from $50 to $200, balancing cost with robust protection.

Hardware Wallets – Discover all Ledger Hardware Wallets | Ledger
Comparing Software and Hardware Cryptocurrency Wallets
Software wallets offer convenience and low cost—often free. They enable seamless integration with DeFi apps and quick swaps. Drawbacks include vulnerability to phishing and device hacks.
Hardware wallets prioritize security, isolating keys from online risks. They’re less convenient for frequent use but essential for substantial portfolios. A hybrid approach: Use software for small amounts and hardware for savings.
In terms of accessibility, software wins for beginners. Hardware demands more setup but provides peace of mind. Both support major assets like Bitcoin and Ethereum.
For visual comparison, here’s an infographic highlighting key differences.

Crypto Wallet Types: Hot vs. Cold & Essential Security Guide | 01
Top Safe Options for Cryptocurrency Wallets
Neutral selections based on reliability include MetaMask for software—widely used for Ethereum interactions. Exodus offers multi-asset support with built-in exchanges.
For hardware, Ledger provides touchscreen interfaces and app integrations. Trezor emphasizes open-source code for transparency. Tangem uses card-like NFC tech, eliminating batteries.
These options score high on security audits and user reviews. Always verify compatibility with your assets.
Setup Steps for Cryptocurrency Wallets
Starting with software: Choose an app like MetaMask. Install via official site. Create a new wallet, note the seed phrase securely (never digitally). Add funds by copying your public address.
For hardware: Unbox devices like Ledger. Connect to a computer, install companion software. Set a PIN, generate and backup the seed phrase offline. Transfer assets from an exchange.
Watch this tutorial for visual guidance: Crypto Wallets Explained (2025 Edition).
Ensure setups occur on trusted networks. Test small transfers first.
Security Best Practices for Cryptocurrency Wallets
Prioritize strong, unique passwords. Enable two-factor authentication (2FA) via apps, not SMS.
Backup seed phrases on metal plates or paper, stored in multiple secure locations. Avoid sharing them.
Use hardware for cold storage. Regularly update software to patch vulnerabilities. Beware phishing—double-check URLs.
For multisig wallets, require multiple approvals for transactions, adding layers against theft.
Monitor addresses via blockchain explorers. If compromised, migrate to a new wallet immediately.
Current Trends and Real-World Relevance
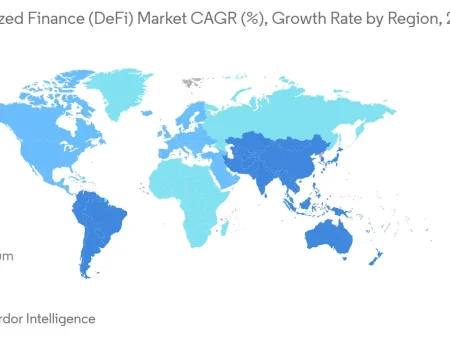
Adoption is booming. In 2025, global crypto users exceeded 500 million, per Chainalysis, driven by institutional interest.
Trends include warm wallets—blending hot convenience with cold security. Integration with fintech apps, like payment systems, expands utility.
Real-world: Wallets enable remittances in emerging markets, bypassing banks. In finance, they facilitate tokenized bonds, appealing to fund managers.
Yet, hacks persist. Personal wallet compromises affected 80,000 victims in 2025, highlighting the need for vigilance.
Here’s a chart on global adoption trends.

Global Crypto Adoption (2026): Users, Rates & Country Data
Pros, Risks, and Common Misconceptions
Pros of software: Speed and accessibility. Hardware: Superior security.
Risks: Software faces malware; hardware, physical loss. Both vulnerable to user error, like lost seeds.
Misconception: Wallets hold crypto. Actually, assets live on the blockchain; wallets manage access.
Another: All hardware is hack-proof. While resistant, supply-chain attacks occur—buy from manufacturers.
Custodial wallets aren’t always bad; they’re fine for small stakes but risk platform failures, as seen in past exchange collapses.
Actionable Insights
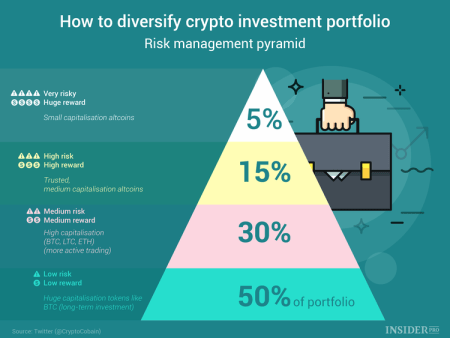
Think holistically: Assess your risk tolerance. Beginners, start with non-custodial software. Scale to hardware as holdings grow.
Watch for updates: Follow sources like CoinDesk for wallet vulnerabilities. Monitor regulations impacting custody.
Do: Diversify storage. Use password managers. Practice recoveries annually.
Avoid rushing setups. Research before integrating with DeFi.
Conclusion
Cryptocurrency wallets evolve, balancing innovation with security demands. In 2026, choosing between software and hardware hinges on your needs—convenience or fortification. Embracing best practices ensures long-term resilience in this volatile space. As blockchain matures, self-custody empowers investors, fostering independence.
What if the next big hack targets unprepared users—will you be ready?
Top Ten References
- Kaspersky: Crypto wallets Explained: Hot vs Cold Wallet vs Hardware Wallet
- Codewave: How Cryptocurrency Wallets Keep Your Funds Moving in 2026
- Money.com: 8 Best Crypto Wallets of January 2026
- Komodo Platform: Choosing Between Hardware Wallet vs Software Wallet
- Chainalysis: 2025 Crypto Theft Reaches $3.4 Billion
- Hacken.io: Wallet Security: Best Practices For Keeping Your Crypto Safe
- Bitcoin.org: Securing your wallet
- Charles Schwab: How to Keep a Crypto Wallet and Keys Secure
- NerdWallet: 9 Best Crypto Wallets for 2026
- Investopedia: Best Crypto Software Wallets for January 2026
(Note: This is not financial advice. Crypto is volatile; always DYOR and only invest what you can afford to lose.)